A New Deal For Hackers
Cracking computers to steal credit cards is pass. Hackers now sell their best tricks to government spies at six-figure prices


At a Google-run competition in Vancouver last month the search giant’s famously secure Chrome web browser fell to hackers twice. Both of the new methods used a rigged website to bypass Chrome’s security protections and completely hijack a target computer. But while those two hacks defeated the company’s defences, it was only a third one that actually managed to get under Google’s skin.
A team of hackers from French security firm Vupen were playing by different rules. They declined to enter Google’s contest and instead dismantled Chrome’s security to win an HP-sponsored hackathon at the same conference. And while Google paid a $60,000 award to each of the two hackers who won its event on the condition that they tell Google every detail of their attacks and help the company fix the vulnerabilities they had used, Vupen’s chief executive and lead hacker, Chaouki Bekrar, says his company never had any intention of telling Google its secret techniques—certainly not for $60,000 in chump change. “We wouldn’t share this with Google for even $1 million,” says Bekrar. “We don’t want to give them any knowledge that can help them in fixing this exploit or other similar exploits. We want to keep this for our customers.”
Those customers, after all, don’t aim to fix Google’s security bugs or those of any other commercial software vendor. They’re government agencies who purchase such “zero-day” exploits, or hacking techniques that use undisclosed flaws in software, with the explicit intention of invading or disrupting the computers and phones of crime suspects and intelligence targets.
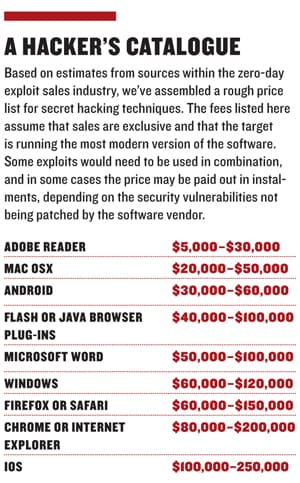
In that shady but legal market for security vulnerabilities, a zero-day exploit that might earn a hacker $2,000 or $3,000 from a software firm could earn 10 or even 100 times that sum from the spies and cops who aim to use it in secret. Bekrar won’t detail Vupen’s exact pricing, but analysts at Frost & Sullivan, which named Vupen the 2011 Entrepreneurial Company of the Year in vulnerability research, say that Vupen’s clients pay around $100,000 annually for a subscription plan, which gives them the privilege of shopping for Vupen’s techniques. Those intrusion methods include attacks on software such as Microsoft Word, Adobe Reader, Google’s Android, Apple’s iOS operating systems and many more—Vupen bragged at HP’s hacking competition that it had exploits ready for every major browser. And sources familiar with the company’s business say that a single technique from its catalogue often costs far more than its six-figure subscription fee. Even at those prices, Vupen hawks each trick to multiple government agencies, a business model that often plays its customers against one another as they try to keep up in an espionage arms race.
Bekrar claims that it carefully screens its clients, selling only to NATO governments and “NATO partners”. He says Vupen has further “internal processes” to filter out nondemocratic nations and requires buyers to sign contracts that they won’t reveal or resell their exploits. But even so, he admits that the company’s digital attack methods could still fall into the wrong hands. “We do the best we can to ensure it won’t go outside that agency,” Bekrar says. “But if you sell weapons to someone, there’s no way to ensure that they won’t sell to another agency.”
That arms-trade comparison is one Vupen’s critics are eager to echo. Chris Soghoian, a privacy activist and fellow at the Open Society Foundations, calls Vupen a “modern-day merchant of death”, selling “the bullets for cyberwar”. After one of its exploits is sold, Soghoian says, “it disappears down a black hole, and they have no idea how it’s being used, with or without a warrant, or whether it’s violating human rights.” The problem was starkly illustrated last year when surveillance gear from Blue Coat Systems of Sunnyvale, California was sold to a United Arab Emirates firm but eventually ended up tracking political dissidents in Syria. “Vupen doesn’t know how their exploits are used, and they probably don’t want to know. As long as the cheque clears.”
Vupen is hardly alone in the exploit-selling game, but other firms that buy and sell hacking techniques, including Netragard, Endgame and larger contractors like Northrop Grumman and Raytheon, are far more tight-lipped than Bekrar’s small firm in Montpellier, France. Bekrar describes his company as “transparent”. Soghoian calls it “shameless”.
Bekrar won’t share revenue numbers, though he insists the firm is profitable. One person who will share those sales numbers is a South African hacker who goes by the name “the Grugq” and lives in Bangkok. For just over a year the Grugq has been supplementing his salary as a security researcher by acting as a broker for high-end exploits, connecting his hacker friends with buyers among his government contacts. He says he takes a 15 percent commission on sales and is on track to earn more than $1 million from the deals this year. “I refuse to deal with anything below mid-five-figures these days,” he says. In December of last year alone he earned $250,000 from his government buyers. “The end-of-year budget burnout was awesome.”But the Grugq assesses Bekrar’s startup, which generates all its own exploits, as significantly more lucrative. “He’s pretty f---ing smart,” says the Grugq. “He holds all the cards. He can tell his clients to buy at the price he’s offering, or someone else will.”
Despite his talk about “transparency”, Bekrar won’t say much about his personal history or career prior to founding Vupen—not even his age. But Vupen is his third try at a startup focussed on digging up software-security bugs. His previous companies, K-Otik and FrSIRT, made their bug findings public. Even after founding Vupen (whose name stands for “vulnerability research” and “penetration testing”) in 2008, Bekrar and his researchers initially worked with some software vendors to patch their flaws. But after taking $1.5 million in venture capital from 360 Capital Partners and Gant & Partners, Bekrar found that the firm could earn far more by keeping its findings under wraps and selling them at a premium.
Lately Bekrar goes so far as publicly taunting the companies whose products he hacks. In May 2011 Vupen released a video showing that it could penetrate a machine running Chrome but offered no further information to Google. When Google responded that Vupen’s exploit targeted the Flash plug-in that runs in the browser rather than Chrome itself, Bekrar accused the company on Twitter of downplaying its vulnerabilities and called it “pathetic”. Google security staffers responded by scolding Bekrar for disregarding users’ privacy and called him an “ethically challenged opportunist.”
Bekrar shrugs off the insults. “We don’t work as hard as we do to help multibillion-dollar software companies make their code secure,” he says. “If we wanted to volunteer, we’d help the homeless.”
First Published: Apr 19, 2012, 06:22
Subscribe Now